
A newly discovered phishing-as-a-service (PhaaS) platform, named VoidProxy, targets Microsoft 365 and Google accounts, including those protected by third-party single sign-on (SSO) providers such as Okta.
The platform uses adversary-in-the-middle (AitM) tactics to steal credentials, multi-factor authentication (MFA) codes, and session cookies in real time.
VoidProxy was discovered by Okta Threat Intelligence researchers, who describe it as scalable, evasive, and sophisticated.
The attack begins with emails from a compromised accounts at email service providers, like Constant Contact, Active Campaign, and NotifyVisitors, whicch include shortened links that send recipients to phishing sites after a multiple redirections.
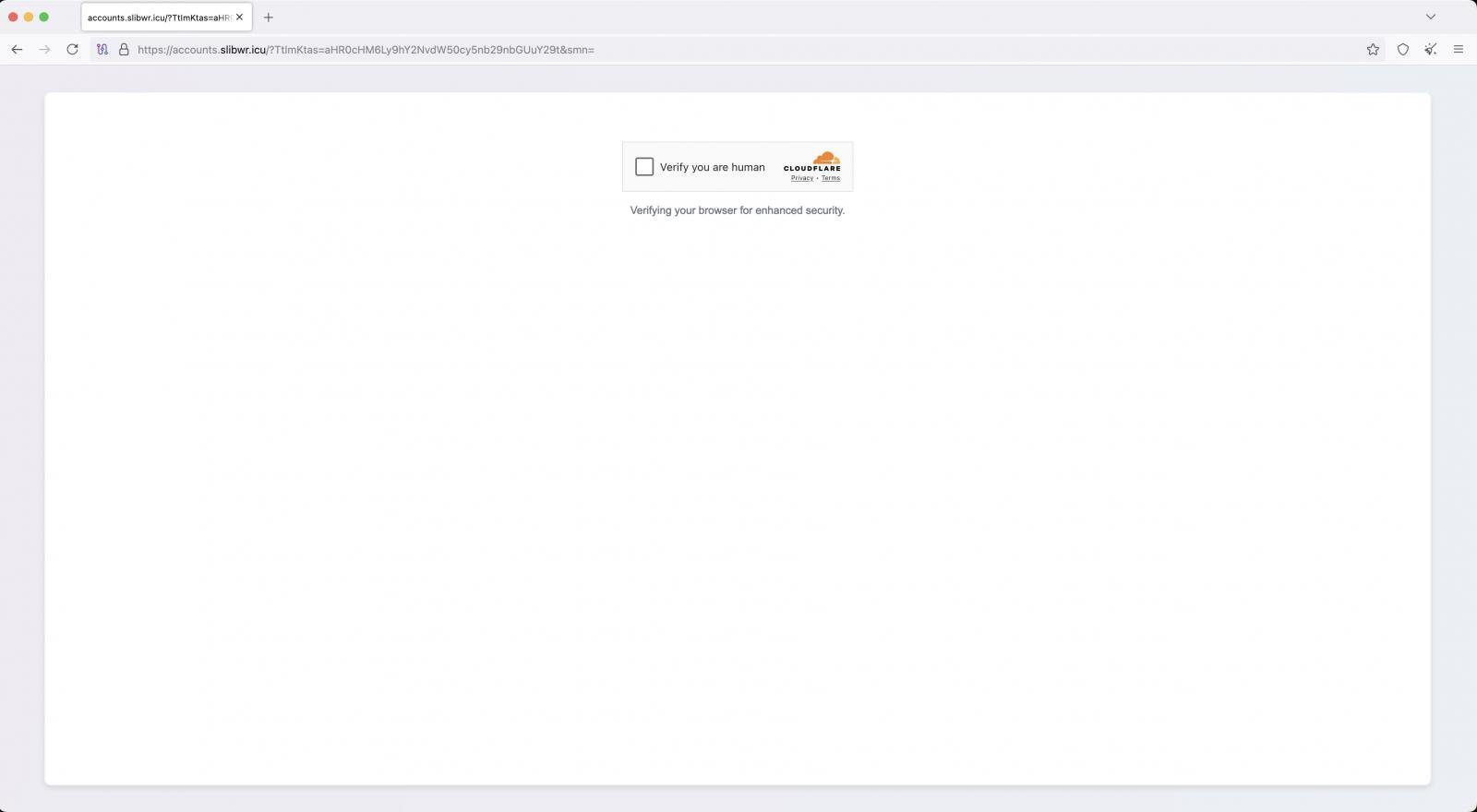
The malicious sites are hosted on disposable low-cost domains on .icu, .sbs, .cfd, .xyz, .top, and .home, which are protected by Cloudflare to hide their real IPs.
Visitors are first served a Cloudflare CAPTCHA challenge to filter out bots and increase the sense of legitimacy, while a Cloudflare Worker environment is used to filter traffic and load pages.
Source: Okta
Selected targets revceive a page that mimics a Microsoft or Google login, while the rest are funneled to a generic and “Welcome” page that presents no threat.
If credentials are typed into the phishing form, requests are proxied through VoidProxy’s adversary-in-the-middle (AitM) to Google or Microsoft servers.
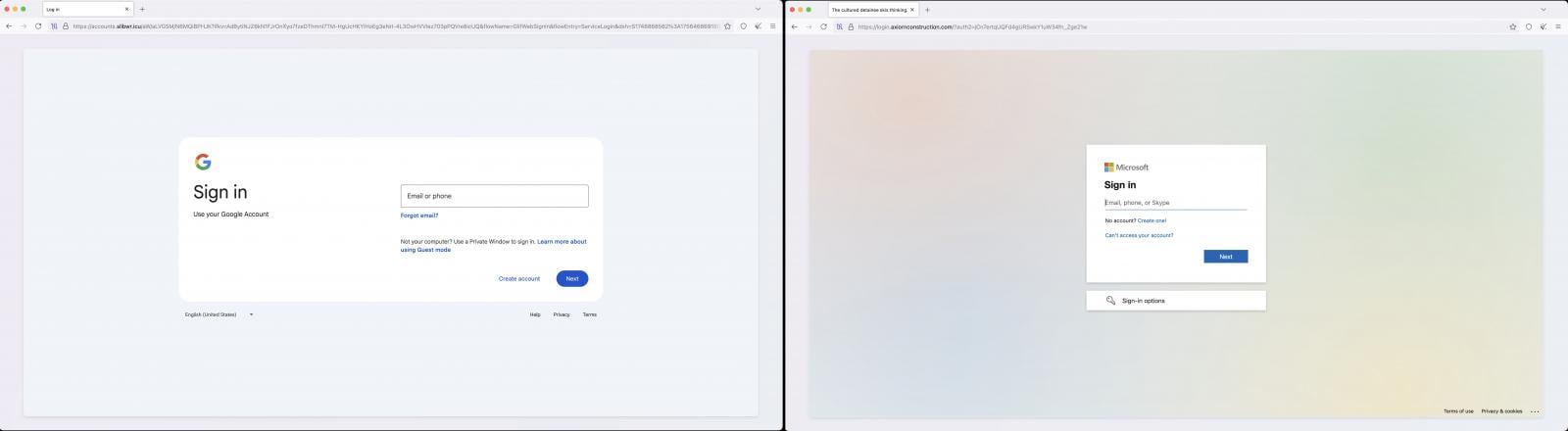
Source: Okta
Federated accounts like those using Okta for SSO are redirected to a second-stage phishing page impersonating Microsoft 365 or Google SSO flows with Okta. These requests were proxied to Okta servers.
The service’s proxy server relays traffic between the victim and the legitimate service while capturing usernames, passwords, and MFA codes in transit.
When the legitimate service issues a session cookie, VoidProxy intercepts it and creates a copy that is made available to the attackers right on the platform’s admin panel.

Source: Okta
Okta noted that users who had enrolled in phishing-resistant authentications like Okta FastPass were protected from VoidProxy’s attack flow and received warnings about their account being under attack.
The researchers recommendations include restricting access of sensitive apps only to managed devices, enforcing risk-based access controls, using IP session binding for administrative apps, and forcing re-authentication for admins attempting sensitive actions.

46% of environments had passwords cracked, nearly doubling from 25% last year.
Get the Picus Blue Report 2025 now for a comprehensive look at more findings on prevention, detection, and data exfiltration trends.
